Cyber security and Ethical Hacking
Cyber security and Ethical Hacking
Cybersecurity and Ethical Hacking (CEH) is a structured, 20-day intermediate training programme designed for participants with a basic IT-related background. The course prioritizes a blend of core security concepts and practical application, progressing from infrastructure fundamentals to offensive methodologies, defensive tooling, and incident response. Each session is designed as a 3-hour block, combining conceptual instruction with hands-on applications to ensure learners can map threats, audit systems, and implement defenses effectively.
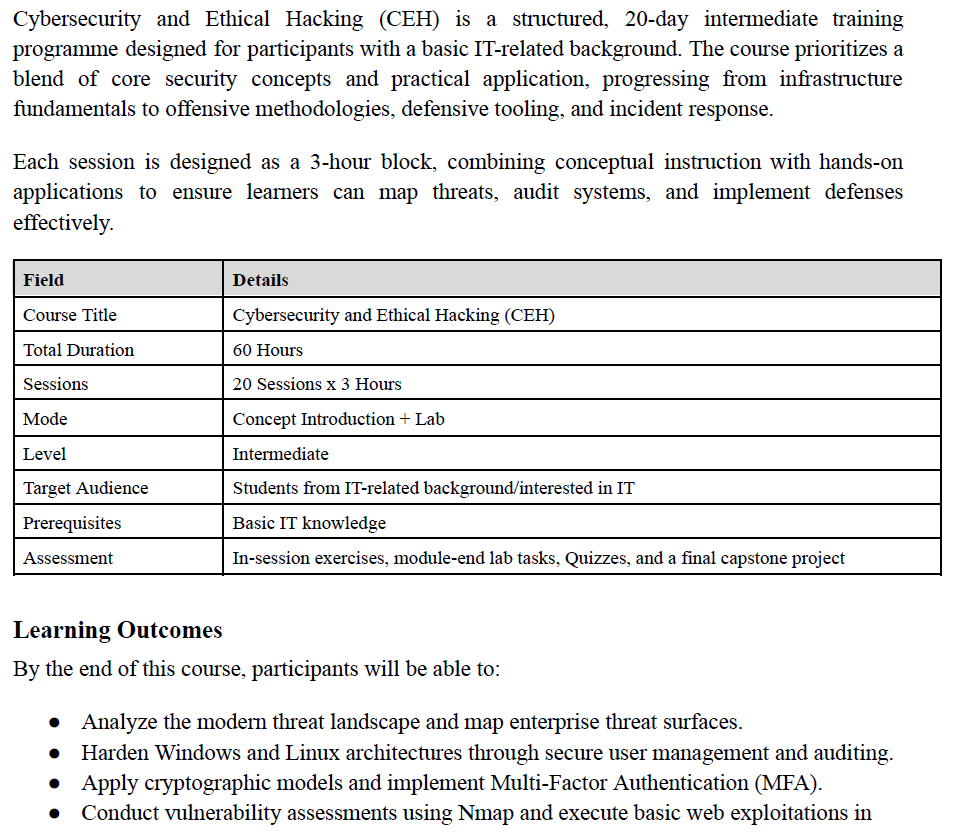
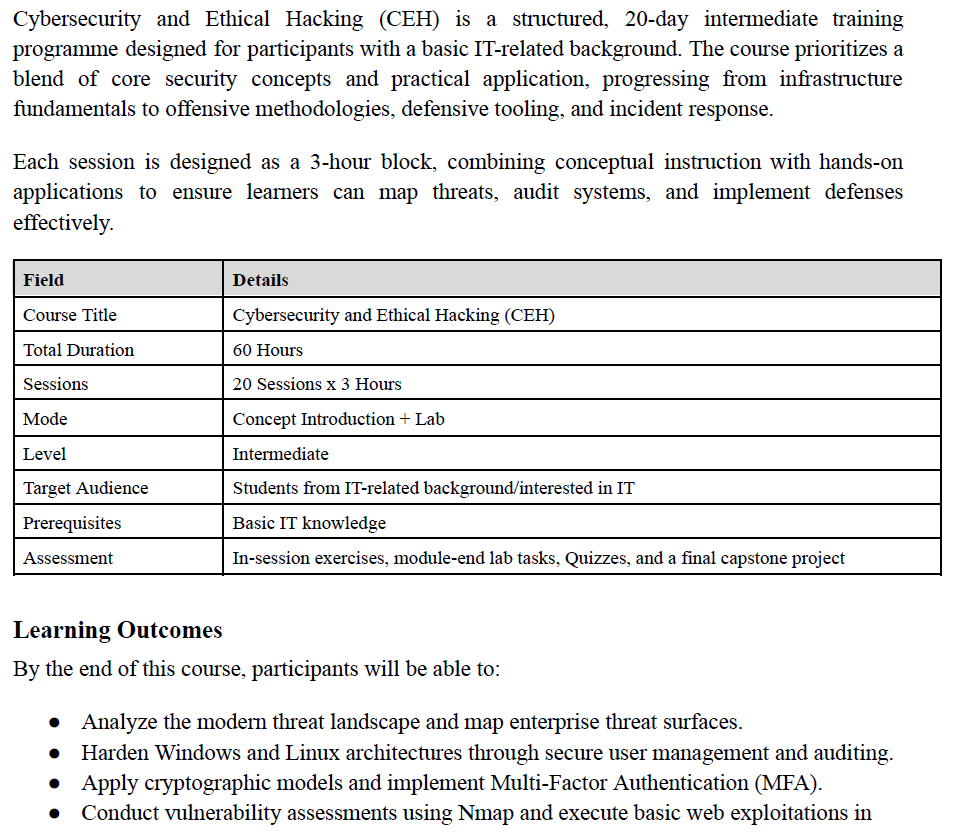
Course Overview
Cybersecurity and Ethical Hacking (CEH) is a structured, 20-day intermediate training programme designed for participants with a basic IT-related background. The course prioritizes a blend of core security concepts and practical application, progressing from infrastructure fundamentals to offensive methodologies, defensive tooling, and incident response.
Each session is designed as a 3-hour block, combining conceptual instruction with hands-on applications to ensure learners can map threats, audit systems, and implement defenses effectively.
Field
Details
Course Title
Cybersecurity and Ethical Hacking (CEH)
Total Duration
60 Hours
Sessions
20 Sessions x 3 Hours
Mode
Concept Introduction + Lab
Level
Intermediate
Target Audience
Students from IT-related background/interested in IT
Prerequisites
Basic IT knowledge
Assessment
In-session exercises, module-end lab tasks, Quizzes, and a final capstone project
Learning Outcomes
By the end of this course, participants will be able to:
● Analyze the modern threat landscape and map enterprise threat surfaces.
● Harden Windows and Linux architectures through secure user management and auditing.
● Apply cryptographic models and implement Multi-Factor Authentication (MFA).
● Conduct vulnerability assessments using Nmap and execute basic web exploitations in controlled environments.
● Utilize AI-driven security concepts and navigate the Incident Response (IR) lifecycle.
Course Modules 1
The course is divided into five modules that progress from foundational infrastructure to advanced exploitation and forensic response:
1. Module 1: Infrastructure & Core Security (4 Sessions, 12 Hours)
2. Module 2: Cryptography & Human Factors (4 Sessions, 12 Hours)
3. Module 3: Midterm & Offensive Methodology (4 Sessions, 12 Hours)
4. Module 4: Exploitation, Defense & Cloud (4 Sessions, 12 Hours)
5. Module 5: Response, Forensics & Final Assessment (4 Sessions, 12 Hours)
Course Structure (60 Hours — 20 Sessions)
No.
Module
Topics
Sessions
Hours
Type
1
Infrastructure & Core Security
CIA Triad; Network Architecture; Windows/Linux Hardening
4
12
Concept + Lab
2
Cryptography & Human Factors
PKI; Password Cracking; Social Engineering; Malware Analysis
4
12
Concept + Lab
3
Midterm & Offensive Methodology
Midterm Exam; Reconnaissance; VAPT (Nmap); Web Architecture
4
12
Concept + Lab
4
Exploitation, Defense & Cloud
SQLi/XSS; Firewalls & EDR; AI in Cyber; Cloud Security
4
12
Concept + Lab
5
Response, Forensics & Ethics
Incident Response; Digital Forensics; Governance; Final Exam
4
12
Concept + Lab
—
Total
—
20
60
—
Module 1: Infrastructure & Core Security
Module 1 establishes the foundational pillars of security, starting with the CIA triad and moving into the practicalities of how systems communicate and are secured at the OS level.
Session 1: Modern Threat Landscape (3 Hours)
● Concepts: CIA Triad (Confidentiality, Integrity, Availability); APTs, script kiddies, and organized hacker groups; Physical and Operational Security (OPSEC).
● Application: Mapping the threat surface of a mid-sized enterprise based on a case study.
Session 2: Network Architecture (3 Hours) 2
● Concepts: MAC addresses, IP addressing, and DNS architecture; Simplified OSI Model for defense.
● Hands-on: Building a virtual network and using ping, tracert, and ipconfig/ifconfig to map topology.
Session 3: Windows Security Architecture (3 Hours)
● Concepts: Advanced UAC, NTFS permissions, and Active Directory; Windows Registry and event logs.
● Application: Auditing Windows event logs to identify suspicious login patterns and privilege escalation.
Session 4: Linux Security Fundamentals (3 Hours)
● Concepts: Linux CLI administration; File permissions (chmod/chown) and secure user management.
● Hands-on: Hardening an Ubuntu machine and enforcing secure permission structures.
Module 2: Cryptography & Human Factors
This module explores the mathematical protections of data and the psychological vulnerabilities of the people using those systems.
Session 5: Applied Cryptography (3 Hours)
● Concepts: Hashing (MD5, SHA-256) vs. Encryption; Symmetric vs. Asymmetric models; SSL/HTTPS; Quantum threats.
● Application: Implementing a basic PKI and generating certificates.
Session 6: Access Control & Authentication (Practical) (3 Hours)
● Concepts: MFA, biometric controls, and enterprise password managers.
● Hands-on: Password cracking with Hashcat or John the Ripper to understand weak password failures.
Session 7: The Human Element & Social Engineering (3 Hours)
● Concepts: Phishing, spear-phishing, vishing, and baiting; The psychology of manipulation.
● Application: Designing a simulated social engineering awareness campaign.
Session 8: Malware Anatomy & Analysis (Practical) (3 Hours) 3
● Concepts: Distinguishing Viruses, Worms, Trojans, and Ransomware.
● Hands-on: Phishing header analysis; Safely detonating a mock-virus in a controlled sandbox.
Module 3: Midterm & Offensive Methodology
Module 3 bridges theoretical knowledge with the structured approach used by attackers to find and analyze vulnerabilities.
Session 9: Midterm Examination (3 Hours)
● Assessment: Comprehensive MCQ covering Modules 1 and 2 (Networking, OS, Cryptography, and Malware).
Session 10: The Hacker Methodology (3 Hours)
● Concepts: Phases of an attack: Reconnaissance, Scanning, Gaining/Maintaining Access, Clearing Tracks; Evasion methods; Passive vs. Active reconnaissance.
● Application: Performing passive reconnaissance using OSINT tools.
Session 11: Vulnerability Assessment and Penetration Testing (3 Hours)
● Concepts: VAPT fundamentals; Network ports and protocols (TCP vs. UDP).
● Hands-on: Utilizing Nmap to scan networks, identify live hosts, and enumerate services for vulnerabilities.
Session 12: Web Application Architecture & Vulnerabilities (3 Hours)
● Concepts: HTTP request/response cycle; Secure cookie management; Introduction to OWASP Top 10.
● Application: Intercepting and analyzing web traffic using Burp Suite.
Module 4: Exploitation, Defense & Cloud
Participants learn to execute common web attacks and configure modern defensive tools, including AI-enhanced security.
Session 13: Basic Web Exploitation (Practical) (3 Hours)
● Concepts: Mechanics of SQL Injection (SQLi) and Cross-Site Scripting (XSS).
● Hands-on: Executing SQLi and XSS payloads on the DVWA platform. 4
Session 14: Defensive Tooling: Firewalls & EDR (3 Hours)
● Concepts: Stateful inspection firewalls; Evolution from Antivirus to EDR behavioral detection.
● Hands-on: Configuring UFW or Windows Defender Firewall with custom rules.
Session 15: AI in Cybersecurity (Practical) (3 Hours)
● Concepts: ML models for anomaly detection; Adversarial ML and data poisoning.
● Application: Demonstrating data poisoning on a simplified ML model.
Session 16: